L0phtcrack 6 Cracked
L0phtcrack6CrackedAircrack ng. Blog post KRACK WPA Vulnerability Key Reinstallation Atta. CK 1. 6 Oct 1. 7. In this blog post. Excel Password Unlocker v4. PATCH Forgot your Excel password and cannot open the file Windows Password Unlocker can help you effectively recover. KRACK vulnerability is explained a brief summary, whos affected, what to do and links to resources related to the vulnerability. TL DR Another day, another vulnerability, just patch your systems. It allows decryption of traffic but does not disclose the WPA key. Blog post On drivers, rtl. Versapro 2 04 Software Update. WN7. 22. N, monitor mode, QCA6. Aug 1. 7. In this blog post. L0phtcrack 6 Cracked' title='L0phtcrack 6 Cracked' />Wi Fi topics using drivers, driver development, embedded chipsets, 8. QCA6. 17. 4, linux backports aka compat wireless and some other good news. Dictionary attack Wikipedia. In cryptanalysis and computer security, a dictionary attack is a technique for defeating a cipher or authentication mechanism by trying to determine its decryption key or passphrase by trying hundreds or sometimes millions of likely possibilities, such as words in a dictionary. TechniqueeditA dictionary attack is based on trying all the strings in a pre arranged listing, typically derived from a list of words such as in a dictionary hence the phrase dictionary attack. In contrast to a brute force attack, where a large proportion of the key space is searched systematically, a dictionary attack tries only those possibilities which are deemed most likely to succeed. Dictionary attacks often succeed because many people have a tendency to choose short passwords that are ordinary words or common passwords, or simple variants obtained, for example, by appending a digit or punctuation character. Dictionary attacks are relatively easy to defeat, e. Install Winpcap Without Admin Rights On Windows. Pre computed dictionary attackRainbow table attackeditIt is possible to achieve a timespace tradeoff by pre computing a list of hashes of dictionary words, and storing these in a database using the hash as the key. This requires a considerable amount of preparation time, but allows the actual attack to be executed faster. The storage requirements for the pre computed tables were once a major cost, but are less of an issue today because of the low cost of disk storage. Pre computed dictionary attacks are particularly effective when a large number of passwords are to be cracked. The pre computed dictionary need be generated only once, and when it is completed, password hashes can be looked up almost instantly at any time to find the corresponding password. A more refined approach involves the use of rainbow tables, which reduce storage requirements at the cost of slightly longer lookup times. See. LM hash for an example of an authentication system compromised by such an attack. Pre computed dictionary attacks, or rainbow table attacks, can be thwarted by the use of salt, a technique that forces the hash dictionary to be recomputed for each password sought, making precomputation infeasible, provided the number of possible salt values is large enough. Dictionary attack softwareeditSee alsoeditReferenceseditExternal linksedit. L0phtcrack 6 Cracked' title='L0phtcrack 6 Cracked' />

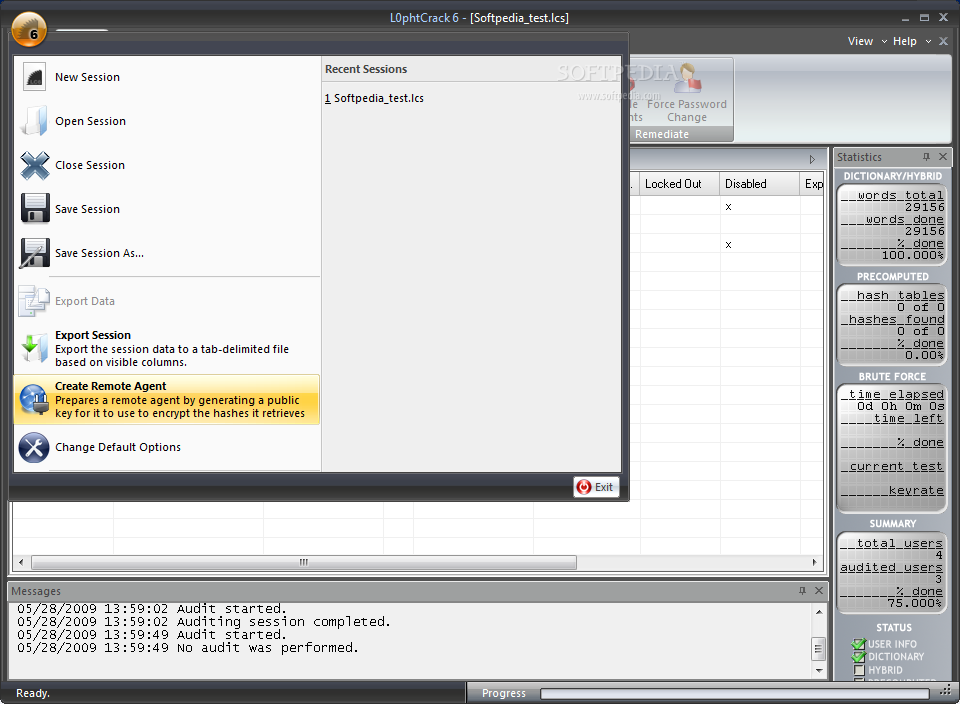 In cryptanalysis and computer security, password cracking is the process of recovering passwords from data that have been stored in or transmitted by a computer system. Ok, the only password cracker you have on here that WAS my favorite is now the most useless. That is L0pht or it was when it was free, it cracked password I thought. Network Footprinting Reconnaissance The tester would attempt to gather as much information as possible about the selected network. Reconnaissance can take two forms.
In cryptanalysis and computer security, password cracking is the process of recovering passwords from data that have been stored in or transmitted by a computer system. Ok, the only password cracker you have on here that WAS my favorite is now the most useless. That is L0pht or it was when it was free, it cracked password I thought. Network Footprinting Reconnaissance The tester would attempt to gather as much information as possible about the selected network. Reconnaissance can take two forms.



